| Generating Your Key Revocation Certificate | |
| Overview | |
| Before we plunge into the actual step-by-step
process of generating a key revocation certificate, let's describe
briefly what we'll do.
First, we'll open PGPkeys and disable keyserver updating (we don't want the keyservers to be updated when we revoke our key). Then we'll export our key pair (both the public and private key) to an ASCII Armored file (.ASC). Next, we'll revoke our key and export the revoked public key to a file -- this is our key revocation certificate. Once we have our key revocation certificate, we can delete the revoked key pair off our key ring and re-import the good (non-revoked) copy of our key pair (which we created earlier). Finally, we'll discuss a few ways to back up and safeguard our key revocation certificate for future use. |
|
| So, let's get started. Almost everything we do here will be through PGPkeys, the PGP key ring management program. | |
| 1. | Open PGPkeys |
| Open PGPkeys from the Start menu or from PGPtray... | |
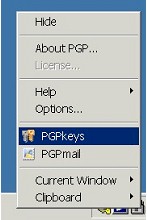 |
|
| PGPkeys will open to the main window, displaying all the keys on your keyring. | |
| 2. | Disable Key Revocation Key Server Updating |
| Before we do anything else, we need to disable PGP's keyserver updating for key revocation. Since we'll be revoking our key in just a bit, we don't want PGP to forward that revocation to the keyservers. | |
| Open PGP's Options from the Edit menu... | |
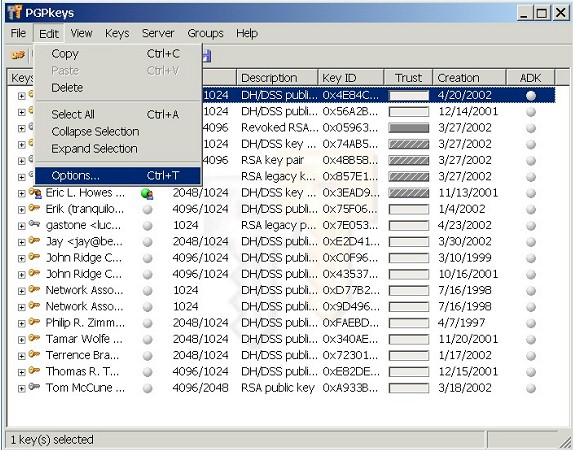 |
|
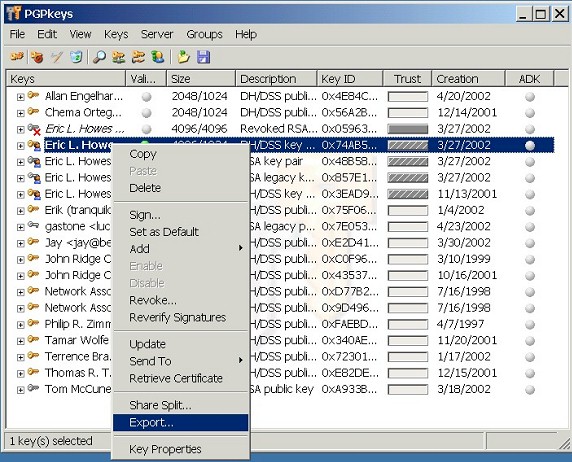
| ...and click on the Servers tab. | |
 |
|
| Make sure the "Revocation" box near the bottom in not checked. It should be unchecked by default, but verify that it is in fact unchecked. After you've done so, click OK to return to the main PGPkeys window. | |
| 3. | Export Your Key Pair |
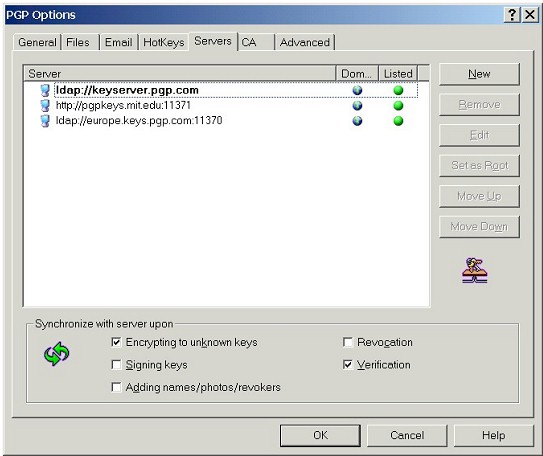
| Before we create the key revocation certificate, we need to back up our key pair so that we can re-import it later. Right-click on your key pair, and select Export... from the context menu. | |
|
|
| Select a directory to export your key pair to. And make sure that you've got the "Include Private Key(s)" box checked (we need both parts of our key pair to be exported). | |
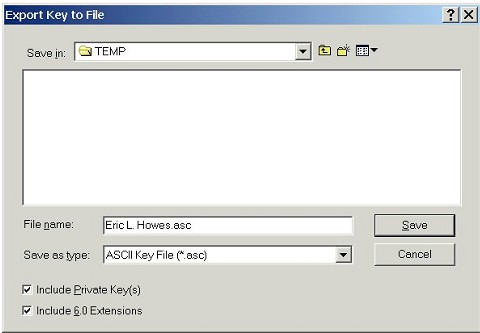
|
|
| Click Save to export your key pair to a ASCII Armored file (.ASC). | |
| 4. | Revoke Your Key |
| Now we can revoke the key and generate the key revocation certificate. Right-click again on your key pair, and select Revoke... from the context menu. | |
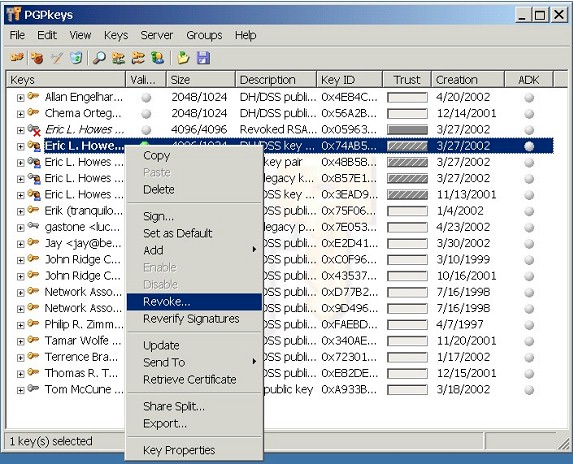
|
|
| PGP confirms that you actually want to revoke your key (click Yes). | |
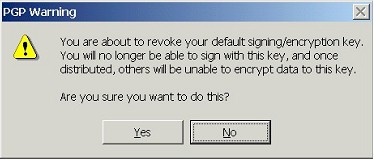
|
|
| Now you'll have to type in your passphrase to unlock your private key and revoke the key. | |
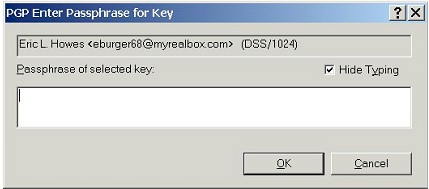
|
|
| Once you've revoked your key, you'll notice that it is designated as "revoked" on your key ring (e.g., "Revoked DH/DSS key pair" under Description). | |
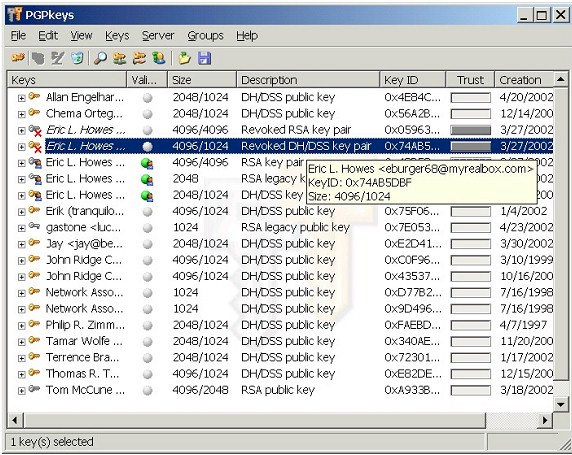
|
|
| If you right-click on the key pair and select Key Properties, you'll see that the properties box for the key pair clearly specifies that the key is revoked. | |
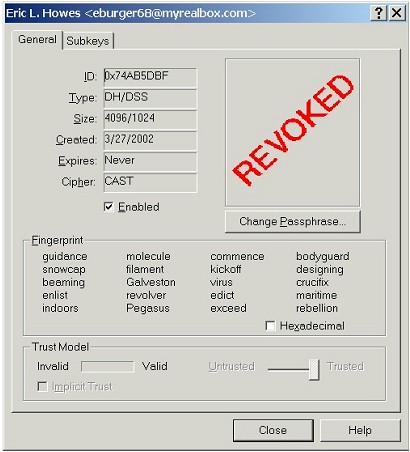
|
|
| Once a key is revoked, it can't be used for encryption. Don't worry, though. In just a bit we're going to re-import our non-revoked key pair (which we created earlier) so that we can continue to use our PGP key pair. | |
| 5. | Export Your Revoked Public Key |
| Now that we've revoked our key, we'll export a copy of the revoked public key to an ASCII Armored file (.ASC). This will be our key revocation certificate which we can store and use in the future. | |
| Right-click on your revoked key pair and select Export... (as we did above when we exported our key pair). This time, however, don't check the "Include Private Key(s)" box -- we're only exporting the public key (such as you do when you distribute your public key to others). | |
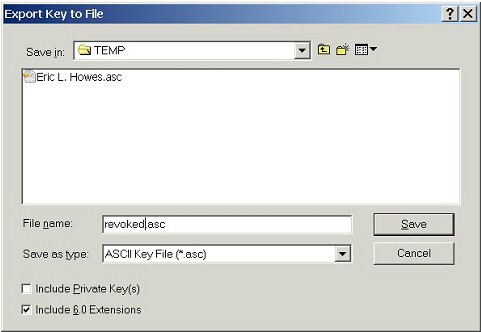
|
|
| Choose a different name for this key file, though (we don't want to overwrite our non-revoked key pair which we exported earlier). Once you click Save, you'll be returned to the main PGPkeys window. | |
| Exporting and Printing Your Key Revocation Certificate | |
| In addition to exporting a key revocation certificate to a file (as we just did), we can also print out a copy of the key revocation certificate. That's an additional layer of insurance, because we could still scan in that hard copy of the key revocation certificate and save it as a ASCII Armored file (.ASC), which is really just a plain text file. | |
| First, copy the revoked public key (which is essentially the key revocation certificate) to the clipboard. Right-click on your key pair and select Copy from the context menu. | |
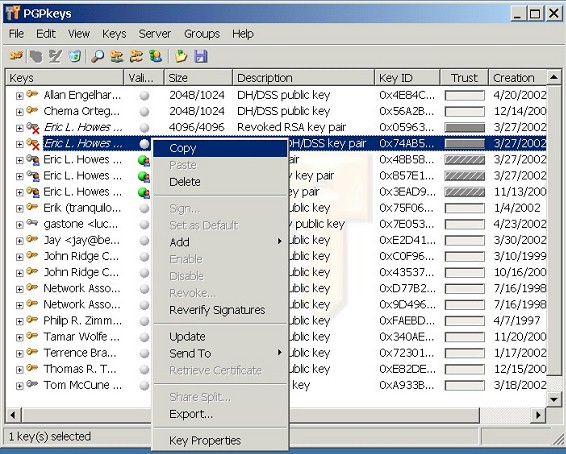
|
|
| Then you can paste your revoked public key into a simple text file (you can use a simple text editor like Notepad). | |
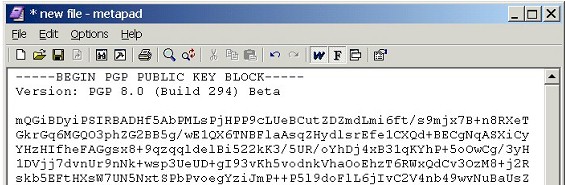
|
|
|
At this point you can print your key revocation certificate and store the
hard copy in a safe place.
Reportedly, a fixed width font like Courier works best for this process. And make sure the font size is big enough (12 pt. minimum). You ought to do testing with your hard copy once you've printed it. Getting an error-free scan can be tricky, so be prepared to do a bit of hand-editing once you scan the revoked key back in. Obviously, this hard copy would be an absolute last resort -- an ultimate fall-back when every other plan failed. |
|
| 6. | Delete Your Revoked Key Pair |
| Now that we have a key revocation certificate saved as an ASCII Armored file (.ASC), we can delete the revoked copy of our key pair off of our key ring and re-import the good (non-revoked) copy. | |
| Right-click on your key pair and select Delete from the context menu. | |
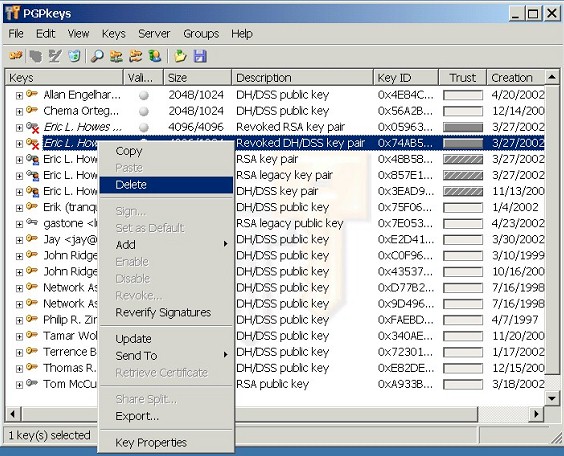 |
|
| PGP will confirm that you actually want to delete the key pair from your key ring (click Yes). | |
 |
|
| Now we're ready to re-import the non-revoked copy of our key pair which we generated earlier. | |
| 7. | Re-import Your (Good) Key Pair |
| Find the file to which you exported your key pair earlier. Double-click on it to import it back on to your key ring. PGP will summarize the keys that you are importing... | |
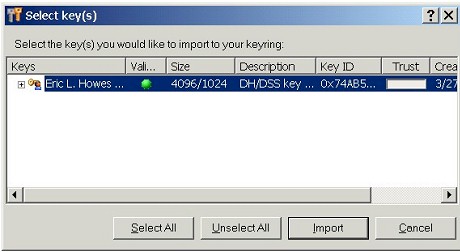 |
|
| ...and notify you that some of the keys are secret keys, for which you'll need to set the Trust level. | |
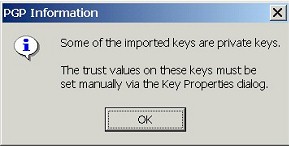 |
|
| To set the proper trust level on our key pair, bring up the Key Properties for that key pair (after you re-import it), and check "Implicit Trust." | |
| At this point you have a key revocation certificate (in the form of an ASCII Armored key file) and you have a non-revoked copy of your key pair back on your key ring. | |
| 8. | Store Your Key Revocation Certificate Securely |
| You should put some thought into how you want to store
your key revocation certificate. Remember: this key revocation
certificate is what you'll use to revoke your key when everything else
goes wrong, so you should store this key revocation certificate in a
safe place.
At the very least you ought to move it to some form of removable media (floppy, CD-ROM, ZIP disk, etc.) so that you have it available even if your hard drive fails. If you're using PGP to protect critical or extremely sensitive data, of if you routinely use PGP to digitally sign messages and files to verify their origin and authenticity, then you might even want to consider distributing copies of your key revocation certificate to trusted third parties (known as "designated revokers") or consider storing a copy of your key revocation certificate off-site, perhaps even in a safe deposit box. |
|
| Using Your Key Revocation Certificate | |
| If the time should ever come when you either lose the private key to your key pair or forget the passphrase to the private key, you can use your key revocation certificate to revoke your key. | |
| 1. | Import Your Key Revocation Certificate |
| To import your key revocation certificate onto your key ring (and thus revoke your key), you can either double-click on the key revocation certificate file (.ASC) that you generated earlier, or you can import that file through PGPkeys, as we'll do here. | |
| Within PGPkeys, go Keys >> Import... | |
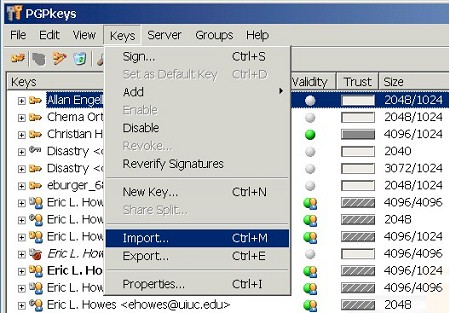 |
|
| Then navigate to the key revocation certificate file and Open it: | |
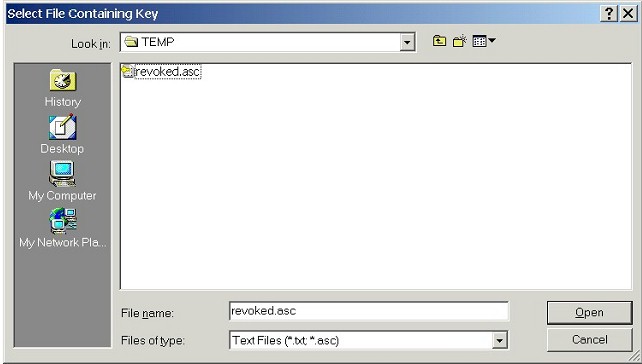 |
|
| PGP displays a summary of the key you will be importing -- notice that it is a "Revoked public key": | |
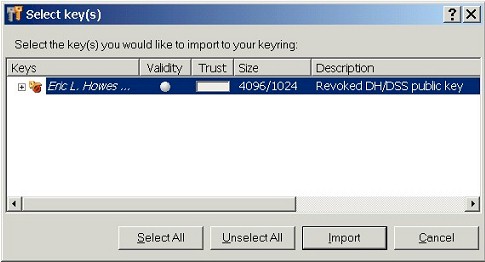 |
|
| Hit the Import button to import this revoked public key (your key revocation certificate) onto your key ring. | |
| Once imported onto your key ring, the affected key will show up as "revoked": | |
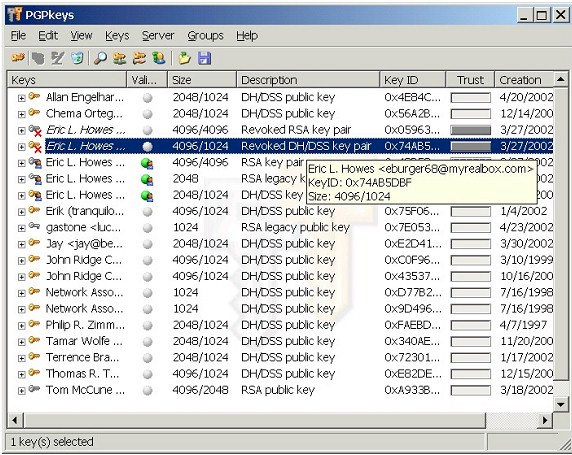 |
|
| And the Key Properties also shows the key revoked: | |
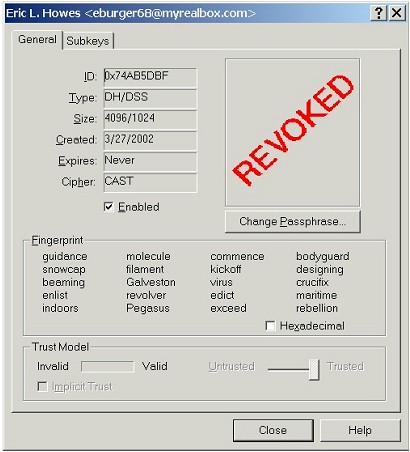 |
|
| 2. | Send Your Revoked Key to Keyservers |
| Now you must upload the revoked key to the keyservers. Within PGPkeys, select (highlight) the revoked key, then go Server >> Send to... | |
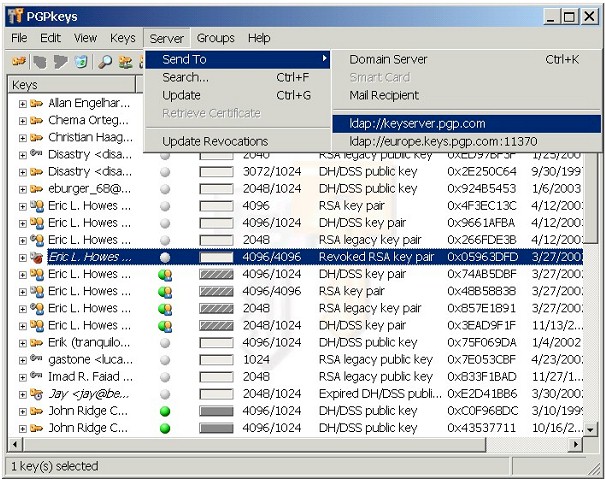 |
|
| ...and select the keyserver to which you want to send your revoked key. | |
| PGP contacts the keyserver you selected... | |
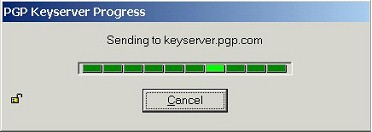 |
|
| ...and notifies you when the revoked key has been uploaded. | |
 |
|
| If you pick one of the larger, more well-used keyservers, most other keyservers will synchronize with it and receive your revoked key within a few days. | |
| People who search for and attempt to retrieve that key from the keyservers will be clearly notified that the key has been revoked, whether they search through PGPkeys or from a web form interface for the keyserver. They will also be able import a revoked copy of your key onto their key rings. More importantly, once your key is marked as revoked on their key rings, PGP will no longer let them use it to encrypt email to you. | |
| 3. | Distribute Your Revoked Key to Email Correspondents |
| Finally, you can distribute your key revocation certificate to people with whom you frequently share PGP-encrypted email. You can send your correspondents the same key revocation certificate file (.ASC) that you imported onto your own key ring. Include a short explanation of why you revoked your key and ask them to import the key revocation certificate onto their own key rings to revoke your key. | |
| You might also consider posting a notice about and copy of the key revocation certificate to web pages from which you might have distributed that key. | |
| Again, once your key is marked as revoked on their key rings, PGP will no longer let your email correspondents use it to encrypt email to you. | |
| Conclusion | |
| I hope you've found this discussion of PGP
key revocation certificates interesting and helpful. I didn't come up
with the idea for this process; I'm merely re-presenting a process that
I've seen described by other people. Two excellent sources for PGP
information and tips are: |
|
| If you're serious about using PGP properly and safely, you owe it to yourself to check out both of these pages and pay close attention to the invaluable advice they offer. | |